Most companies are solving the wrong security problem. They’re building walls when they should be building records.
I spent time studying how the pharmaceutical industry approaches data integrity under FDA’s Current Good Manufacturing Practice (CGMP) regulations — and it fundamentally changed how I think about enterprise security architecture. The lessons aren’t just applicable to biotech or life sciences. They apply to every organization that handles sensitive data, which in 2026, means everyone.
Here’s what the industry gets right that most IT teams still get wrong.
The Perimeter Mindset Is a Liability
Most companies treat security as a perimeter problem — a “wall” to be built around their infrastructure. Firewalls, VPNs, zero-trust network layers. These are necessary, but they are not sufficient.
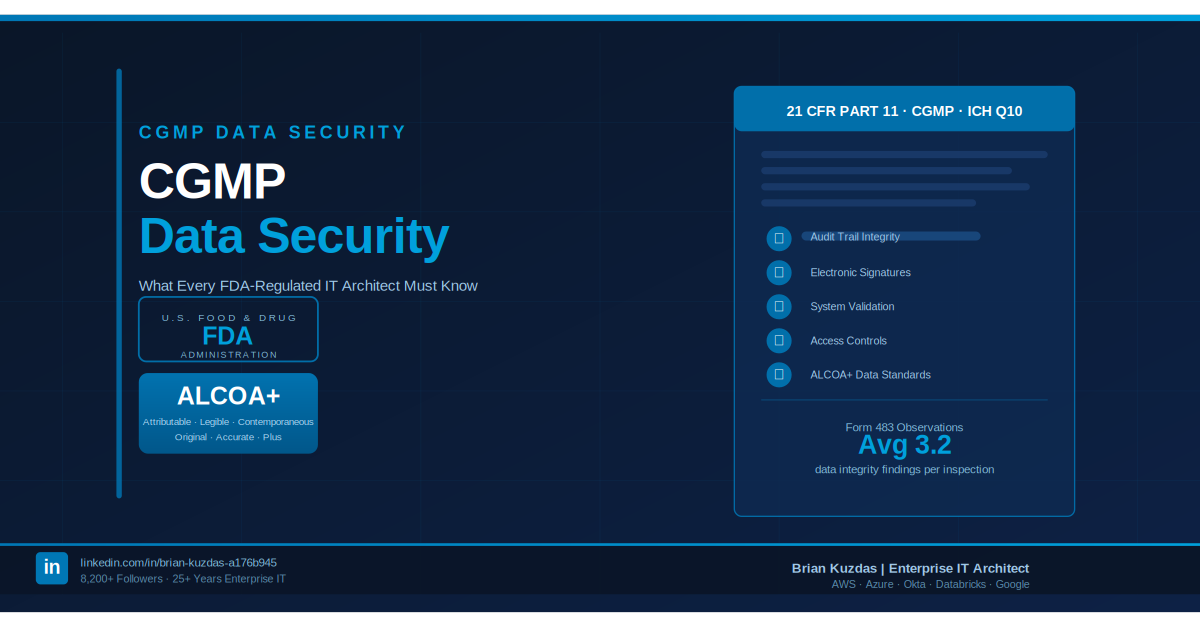
In CGMP, security isn’t just about keeping people out. It’s about the ALCOA+ principle:
- Attributable
- Legible
- Contemporaneous
- Original
- Accurate
The question isn’t “can an attacker get in?” — it’s “can you prove, with certainty, exactly what happened, who did it, and when?”
Most organizations lack that. They have logs — but not a verifiable audit trail of truth. They cannot prove who changed a configuration or accessed a record at a specific microsecond. That gap turns a standard compliance audit into a forensic nightmare, and it transforms minor configuration drift into a catastrophic, invisible vulnerability.
Every Change Is a Batch Record
In pharmaceutical manufacturing, a batch record is a complete, immutable account of every step taken to produce a product. If a step isn’t recorded, it didn’t happen — and the batch is rejected.
Enterprise security needs the same discipline.
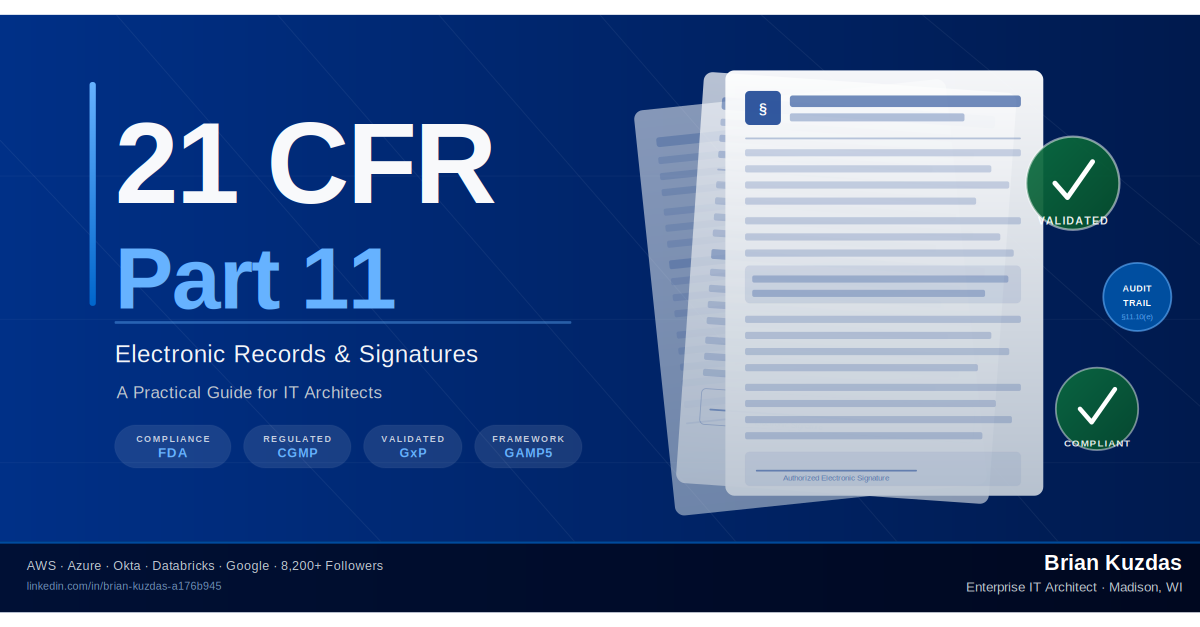
Every infrastructure change, every identity access event, every configuration update must be treated as an immutable, verifiable record. This isn’t just logging — it’s a forensic requirement. Your security architecture must provide a continuous narrative of system state.
This mindset shifts security from a reactive defense posture to a proactive validation culture: any unrecorded action is treated as a potential breach by default. The integrity of the data is preserved throughout its entire lifecycle — not just at the perimeter.
Change Control Is the Antidote to Hero Culture
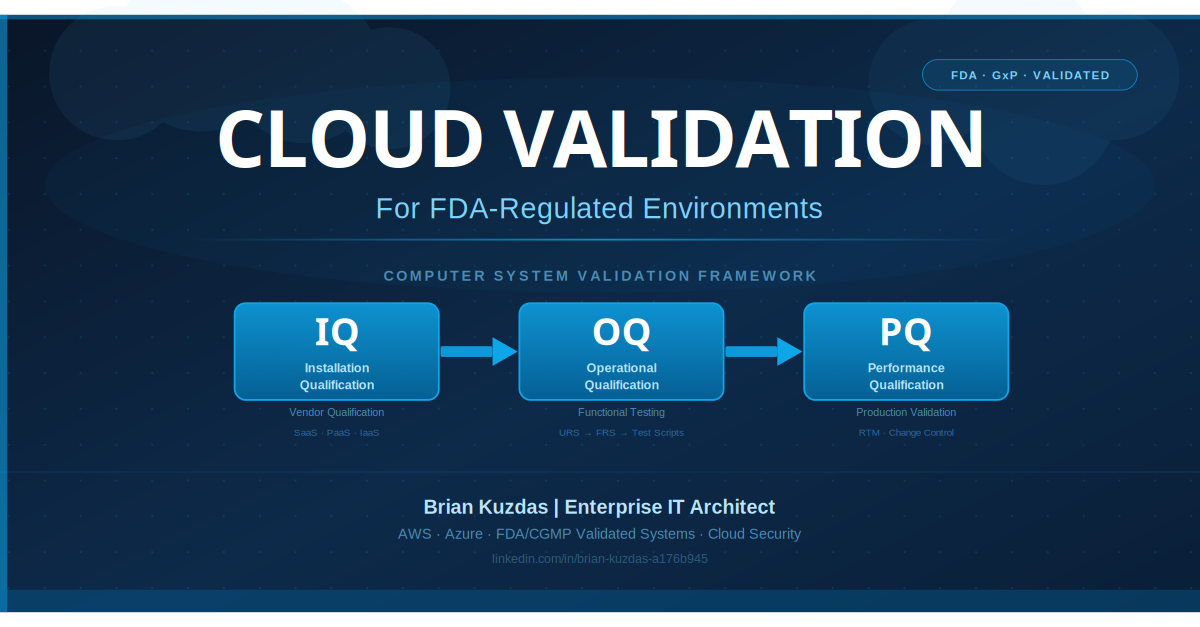
FDA compliance mandates Change Control and Systems Validation — a formal process requiring that every change to a validated system is planned, reviewed, tested, and documented before it touches production.
This is the ultimate antidote to the “hero culture” that plagues IT organizations.
Most security breaches don’t come from sophisticated nation-state attacks. They come from:
- An engineer SSH-ing into production at 2am to “just fix one thing”
- An undocumented manual config change that opened a storage bucket
- A deprecated TLS protocol that nobody noticed because the change was never tracked
By adopting a CGMP mindset, we stop treating infrastructure as a series of one-off tasks and start treating it like a validated manufacturing process. Every deployment is planned, tested, and recorded. The human error that routinely bypasses even the most expensive security software is systematically eliminated.
Validation-as-Code: From Hope-Based to Evidence-Based Security
The final and most powerful shift is moving toward validation-as-code.
Tools like Ansible, Terraform, and Python-based compliance frameworks allow us to treat security configurations the way a pharma company treats a manufacturing process — with absolute reproducibility and a documented evidence package to prove it.
This is the transition from hope-based security (“we think we’re secure”) to evidence-based security (“here is the proof we are secure, continuously”).
Security is no longer a one-time project, a quarterly audit, or a reactive patch. It becomes a continuous, validated state of operation — automatically enforced, automatically verified, automatically documented.
The Bottom Line
CGMP teaches us something deceptively simple: a system is only secure if it performs exactly as intended, every single time, backed by a body of evidence that proves it.
That’s not the mindset most IT organizations operate with. But it should be.
The next time your team debates whether to invest in another firewall appliance or endpoint detection tool, ask yourself first: Can we prove, right now, that our last 100 infrastructure changes were authorized, recorded, and validated?
If the answer is no — that’s where the real vulnerability lives.
Interested in discussing how CGMP principles map to your security architecture? Drop a comment or connect — I’d love to hear how your organization approaches data integrity.
#CyberSecurity #DataIntegrity #CGMP #Compliance #InfrastructureAsCode #EnterpriseIT #ZeroTrust #DevSecOps #RiskManagement #FDACompliance