By Brian Kuzdas | Enterprise IT Architect | AWS · Azure · FDA/CGMP Validated Systems
The Cloud Migration Problem Nobody Talks About
Your CIO just signed a contract to migrate your LIMS to a cloud platform. Your quality team is asking who’s responsible for validation. Your IT team says, “AWS handles the infrastructure.” Your QA manager says, “We still need an IQ/OQ/PQ.” And somewhere in the middle, nobody can answer the central question: what does cloud validation actually look like, and who owns what?
This isn’t hypothetical. As of 2024, more than 60% of life sciences companies have migrated at least one GxP-critical system to a cloud platform. Yet many are still operating under Computer System Validation (CSV) frameworks designed for on-premise software installed in a data center you physically control. The gap between traditional CSV methodology and cloud reality is exactly where FDA 483 observations and warning letters are born.
I’ve worked with regulated companies navigating this exact challenge—from small biotech startups standing up their first cloud-hosted LIMS to large pharmaceutical manufacturers migrating legacy validated systems to AWS or Azure. In every case, the hard conversations happen when someone finally asks: “But what are WE responsible for?”
This article will walk you through what cloud validation actually requires, how the IQ/OQ/PQ framework maps (and critically, doesn’t map) to cloud deployments, and what documentation you need on hand when an FDA investigator walks through your door.
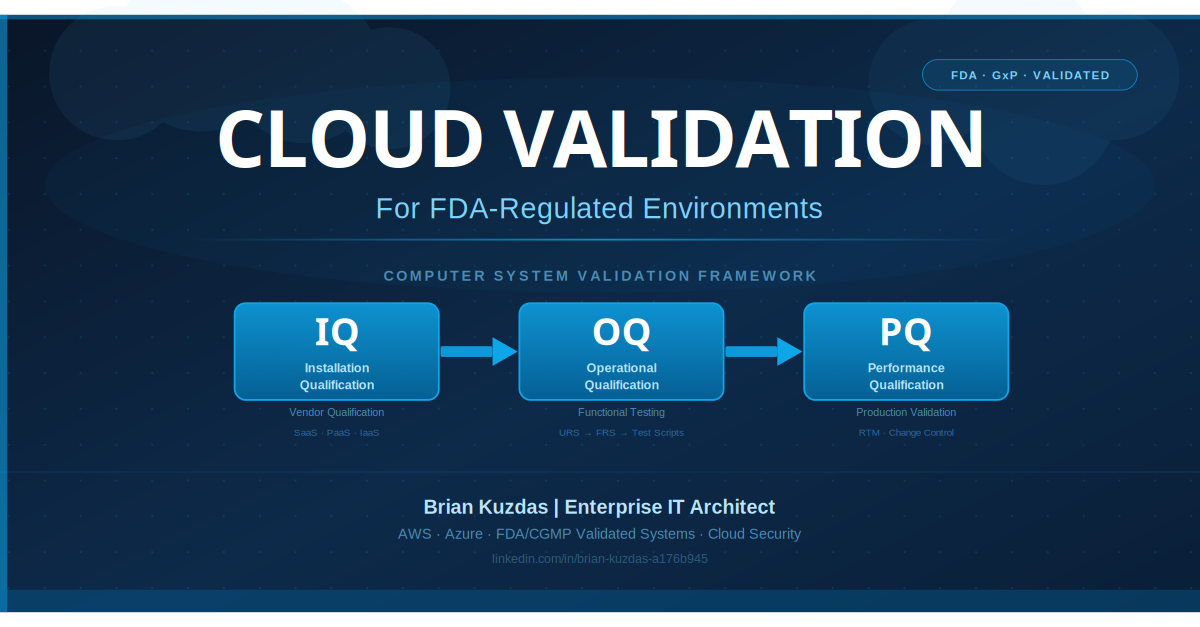
IQ/OQ/PQ in the Cloud Context: Everything Has Changed
The traditional Installation Qualification (IQ), Operational Qualification (OQ), and Performance Qualification (PQ) framework was built around a straightforward model: a vendor delivers software, you install it on hardware you control, you test it against your specifications, and you document every step of the process. The validation package reflects a static, point-in-time installation that you control end to end.
Cloud computing breaks this model in fundamental ways—some obvious, some subtle.
Installation Qualification → Vendor Qualification
Traditional IQ verifies that software was installed correctly on your hardware, to the vendor’s specifications, in your controlled environment. You verify the correct version was installed, the configuration matches approved specifications, and the system meets its physical and software prerequisites.
In a cloud model—particularly SaaS—there is no installation you perform. The software lives on the vendor’s infrastructure, managed by the vendor’s operations team, updated by the vendor’s engineering team. IQ in the cloud context becomes Vendor Qualification: a structured assessment that the vendor’s infrastructure, security controls, development practices, and deployment environment meet the requirements of your validated GxP environment.
Vendor Qualification for a SaaS provider means reviewing:
- SOC 2 Type II reports (and understanding which trust services criteria are in scope)
- ISO 27001 or ISO 27017/27018 certifications
- The vendor’s own Software Development Lifecycle (SDLC) and validation framework
- Data residency and sovereignty documentation
- Business continuity and disaster recovery capabilities
- Subprocessor disclosure and management
This isn’t a checkbox exercise. A completed Vendor Qualification is the foundation of your IQ evidence package for a cloud-hosted system.
Operational Qualification: Largely Unchanged in Concept, Different in Practice
OQ tests that the system functions according to its specifications under controlled conditions—that your User Requirements Specification (URS) requirements are demonstrably met. In cloud, the concept of OQ is unchanged. You still need to test every functional requirement against a documented expected result.
What changes is the execution context. You’re running OQ scripts in a cloud-hosted tenant environment you don’t fully control. The key questions become:
- Does your OQ environment accurately represent your production environment? With cloud infrastructure, this requires careful attention to tenant configuration, network architecture, data residency settings, and integration connections.
- Has the vendor changed the platform between your OQ execution and go-live? SaaS vendors operating on continuous deployment pipelines can—and do—push updates without your explicit consent.
- Are your OQ test environments appropriately segregated? Running OQ in a production tenant, or against production data, is both a regulatory risk and a data integrity problem.
Industry data suggests that 30–40% of first-time cloud OQ executions reveal configuration gaps between the test environment and the intended production environment. Environment equivalence documentation is not optional.
Performance Qualification: Production Reality
PQ verifies that the system performs reliably in the actual production environment under real-world conditions. In cloud, PQ must account for:
- Multi-tenancy effects: Does shared infrastructure introduce latency or inconsistency?
- Internet-dependent connectivity: Is system performance acceptable across the network paths your users will actually use?
- Vendor-side updates during PQ: A SaaS vendor pushing an infrastructure update the day before your PQ execution can invalidate your testing environment.
- SLA guarantees as PQ evidence: Your vendor’s uptime SLA is availability evidence, not performance validation evidence. These are different things.
The critical insight: IQ in the cloud is vendor/infrastructure qualification. OQ and PQ remain entirely your responsibility—executed in your environments, documented in your protocols, signed by your qualified personnel.
The Shared Responsibility Model and What It Actually Means for Validation
AWS, Azure, and Google Cloud all publish a “Shared Responsibility Model” that defines what the Cloud Service Provider (CSP) is responsible for versus what the customer owns. This model is foundational to defining your validation scope.
The CSP is responsible for:
- Physical security of data centers
- Network infrastructure and hardware
- Hypervisor and virtualization layer
- Platform availability and resilience
- Security of the cloud (the infrastructure itself)
You are responsible for:
- Application-level validation
- Data integrity and completeness
- Access controls and identity management
- Audit trail configuration and maintenance
- Change control for application-level changes
- Backup and recovery testing
- GxP regulatory compliance
- Security in the cloud (your application and data)
Here’s the mistake that gets regulated companies into trouble with FDA: they see AWS’s SOC 2 Type II or ISO 27001 certificate and assume it covers their validation obligations. It does not.
AWS’s SOC 2 covers AWS’s internal controls—it demonstrates that AWS manages its own infrastructure securely. It says nothing about your application, your business processes, your audit trails, or your data integrity. The FDA does not audit AWS. They audit you. And when they ask for your IQ/OQ/PQ documentation, presenting an AWS SOC 2 report in place of a validated system protocol will not go well.
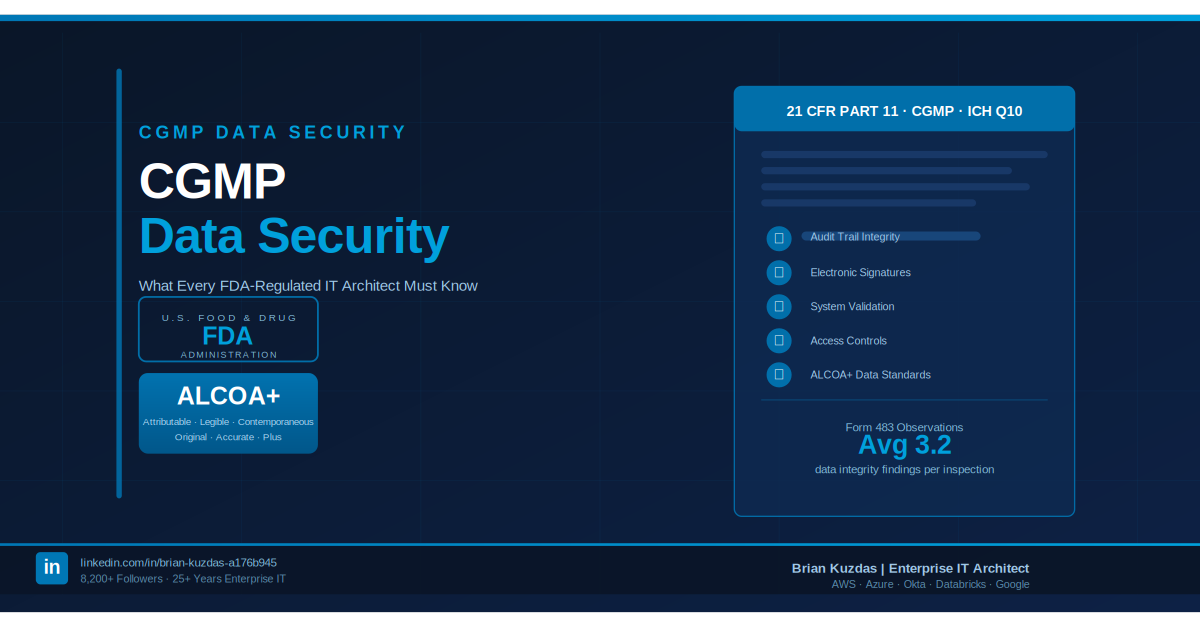
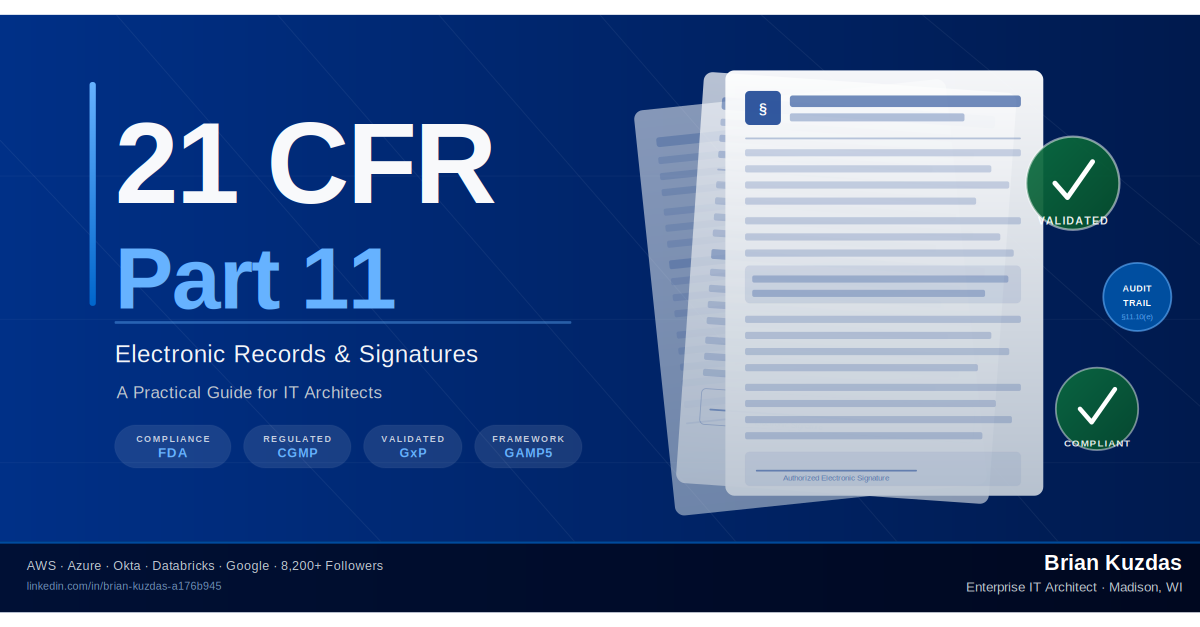
Regulatory Perspective: FDA’s 21 CFR Part 11 requirements for electronic records and electronic signatures apply to your systems and your controls, regardless of where the infrastructure lives. A cloud provider’s certifications are inputs to your vendor qualification—they are not a substitute for your qualification protocols.
FDA has issued multiple 483 observations specifically citing inadequate validation documentation for cloud-hosted systems where companies relied on vendor certifications in place of their own validation activities. The trend is accelerating as cloud adoption grows in regulated industries.
SaaS vs. IaaS vs. PaaS: Validation Scope Differences
Not all cloud service models carry the same validation burden. The model you’re deploying determines how much of the validation stack is yours to own.
Infrastructure as a Service (IaaS): Maximum Validation Scope
With IaaS (AWS EC2, Azure Virtual Machines, Google Compute Engine), you’re renting raw compute, storage, and networking. The CSP manages physical infrastructure and the hypervisor. You manage everything above the virtualization layer: operating system, middleware, application software, configuration, and data.
Validation scope for IaaS: Maximum. You own IQ of the operating system configuration, OQ of the application, PQ in the production environment, and ongoing change control for every layer above the hypervisor. This most closely resembles traditional on-premise validation, with the critical addition of CSP infrastructure qualification documentation as an input to your IQ package.
IaaS validation is the most labor-intensive but also the most familiar to traditional CSV practitioners. The key adaptations are:
- Infrastructure as Code (IaC) using Terraform, CloudFormation, or ARM templates as configuration baseline documentation
- Cloud-native configuration management and drift detection
- CSP-provided audit trails for infrastructure-level events
Platform as a Service (PaaS): Moderate Validation Scope
With PaaS (AWS RDS, Azure App Service, Azure SQL), the CSP manages the underlying OS and middleware in addition to infrastructure. You manage the application and data.
Validation scope for PaaS: Moderate. Your IQ shifts partially to the vendor: you qualify the PaaS service configuration rather than the OS installation. Your OQ and PQ cover your application layer. You inherit the vendor’s change management for the platform layer—but this creates a new obligation: you must have a documented process for assessing the impact of vendor-side platform changes on your validated state.
Software as a Service (SaaS): Minimum but Still Substantial
With SaaS (Veeva Vault, Oracle Cloud ERP, cloud-hosted LIMS platforms), the vendor manages everything from infrastructure to application. You configure and use the software.
Validation scope for SaaS: Minimum—but still substantial. Your IQ becomes vendor qualification plus configuration baseline documentation. Your OQ tests the configured system against your URS. Your PQ validates in the production environment. You still own the RTM, test scripts, change control for configuration changes, and audit trail review procedures.
The SaaS validation trap catches many regulated companies: because the vendor “takes care of everything,” validation feels like the vendor’s problem. It isn’t. Your GxP obligation cannot be delegated. If Veeva Vault stores your controlled documents, your validation of how Veeva Vault is configured, how access is controlled, and how audit trails are maintained—that is yours. Veeva provides their own qualification documentation, which is a valuable input, but it does not replace your validation protocols.
What Your CSP Provides vs. What You Must Create
Let’s be specific about the documentation gap.
What Your CSP Provides (Inputs to Your IQ)
| Document | What It Covers | How to Use It |
|---|---|---|
| SOC 2 Type II Report | CSP internal controls, security, availability | IQ evidence for infrastructure security controls |
| ISO 27001 Certificate | Information security management system | IQ supplemental evidence |
| ISO 27017/27018 | Cloud-specific security, PII in cloud | Supplemental IQ evidence |
| FedRAMP Authorization | US federal compliance framework | Strong evidence for security controls |
| Penetration test summaries | Third-party validation of CSP security | Risk assessment input |
| Physical data center documentation | Physical access controls | IQ physical security section |
| SLA documentation | Availability commitments | PQ availability evidence |
What You Must Create (Cannot Be Delegated)
| Document | Purpose | Notes |
|---|---|---|
| User Requirements Specification (URS) | What the system must do, in business terms | 100% yours; drives all downstream validation |
| Functional Requirements Specification (FRS) | Technical translation of URS | Maps URS requirements to system capabilities |
| Design Qualification (DQ) | System design meets requirements | Configuration baseline, architecture documentation |
| IQ Protocol + Report | Infrastructure/vendor qualification | CSP documentation is input, not substitute |
| OQ Protocol + Report | Functional testing against URS | Your test scripts, your expected results, your signatures |
| PQ Protocol + Report | Production environment validation | Must be executed in production, not test environment |
| Requirements Traceability Matrix (RTM) | Links every requirement to a test case | Auditors look at this closely |
| Validation Plan | Overall approach, scope, methodology | Signed before validation begins |
| Validation Summary Report | Formal conclusion: system is validated | Signed by Quality before production use |
| Change Control SOPs + Records | Maintains validated state | Ongoing requirement, not one-time |
| Audit Trail Review SOP + Records | Periodic audit trail review | 21 CFR Part 11 requirement |
| Periodic Review Records | Ongoing validation maintenance | Typically annual |
Change Management: The Continuous Update Challenge
Traditional CSV was designed around discrete software releases. You validated version 3.2. When the vendor released version 3.3, you ran a change impact assessment, executed a delta qualification, updated your documentation, and closed the change control record. The cycle was measured in months.
Cloud breaks this model at the most fundamental level: SaaS vendors update continuously. Modern cloud-native platforms push updates weekly, sometimes daily. Security patches, performance improvements, UI changes, back-end infrastructure updates—these occur without your explicit consent, and often without detailed advance notice. Under traditional CSV doctrine, every change to a validated system requires an assessment. At cloud velocity, this creates an impossible backlog.
The regulatory framework has adapted—but the underlying expectations have not disappeared. They’ve transformed.
Key Principles for Cloud Change Management
1. Periodic Review Over Discrete Revalidation
Rather than attempting to validate every incremental vendor update, the industry has broadly moved to periodic review cycles—typically quarterly or semi-annual—to assess whether the system remains in a validated state. This requires documented change assessment processes and strong vendor notification agreements.
2. Vendor Change Notification Clauses
Your cloud service agreement must include provisions for advance notice of changes that could affect your validated state. “Material changes” must be defined contractually, and should trigger a documented change impact assessment on your side before the change is implemented in your production tenant.
3. Configuration Baseline Documentation
For SaaS platforms, clearly distinguish what is in your configuration (your tenant, your settings) versus what the vendor controls (platform functionality, infrastructure). Document your configuration baseline as part of your validated state, and route all configuration changes through your change control process.
4. Infrastructure as Code (IaC)
For IaaS and PaaS deployments, implement Infrastructure as Code using Terraform, AWS CloudFormation, or Azure Resource Manager templates. IaC creates a version-controlled, auditable record of your infrastructure configuration—the modern equivalent of a build specification document. Every infrastructure change is a code commit, reviewable and traceable.
5. Configuration Drift Detection
Cloud environments drift from their validated state through accumulated small changes—a modified IAM policy, an adjusted security group rule, an updated parameter. AWS Config, Azure Policy, and CSPM platforms like Prisma Cloud or Wiz can detect configuration drift automatically and trigger your change assessment process.
The FDA’s ongoing expectation under 21 CFR Part 11 and GAMP 5 remains unchanged: you must have a documented, repeatable process for managing changes to validated systems. Cloud velocity doesn’t exempt you—it requires you to be more systematic than ever.
The Complete CSV Documentation Package
When an FDA investigator asks for validation documentation for your cloud-hosted system, here is precisely what you should be able to produce:
Tier 1: Strategic Documents
- Validation Plan — scope, methodology, acceptance criteria, risk assessment, team roles
- Validation Summary Report — formal conclusion of validation completeness, signed by Quality
Tier 2: Requirements Documents
- User Requirements Specification (URS) — business/user requirements, regulatory requirements (21 CFR Part 11 applicability determination)
- Functional Requirements Specification (FRS) — technical requirements mapped from URS
- Design Qualification (DQ) — configuration baseline, architecture diagrams, security architecture
Tier 3: Qualification Protocols and Reports
- IQ Protocol + Executed Report — with vendor qualification documentation as appendix
- OQ Protocol + Executed Report — test scripts with expected results, actual results, deviations, pass/fail
- PQ Protocol + Executed Report — production performance evidence, real user transaction confirmation
Tier 4: Traceability
- Requirements Traceability Matrix (RTM) — every URS requirement → FRS → test case ID → test result
Tier 5: Operational Compliance Records
- Change Control SOP + Records — documented process and evidence of controlled change management
- Audit Trail Review SOP + Completed Reviews — periodic review records per 21 CFR Part 11
- User Access Review Records — evidence of least-privilege enforcement and periodic access review
- Vendor Qualification File — SOC 2 reports, ISO certifications, SLA documentation, change notification agreements
- Periodic Review Records — annual (or more frequent) reassessment of validated state
The FDA’s expectation is not a perfect system. It’s a defensible, documented process that demonstrates you know what your system does, you’ve confirmed it does it correctly, and you know when something has changed.
Bottom Line
Cloud validation is not a shortcut. Moving to a cloud platform does not reduce your validation obligations—it transforms them. The lines of responsibility shift, the documentation sources change, and the change management challenge intensifies. But the core regulatory expectation remains unchanged: you must demonstrate, with documented evidence, that your GxP system does what you say it does.
The good news is that cloud can actually make validation more rigorous and auditable than many on-premise deployments ever were. Infrastructure as Code gives you version-controlled configuration documentation. SOC 2 reports provide pre-existing infrastructure evidence you can cite in your IQ. Cloud-native logging provides audit trail capabilities that often exceed what legacy on-premise systems offered.
The bad news is that most organizations haven’t updated their CSV SOPs to reflect cloud reality—and that gap is exactly what FDA investigators are trained to find.
Practical Takeaways:
- Update your CSV SOPs to explicitly address IaaS, PaaS, and SaaS validation scope differences
- Build vendor qualification into your supplier qualification process—SOC 2 review should be a routine step
- Negotiate change notification provisions into every cloud service agreement
- Implement IaC and configuration drift detection for IaaS/PaaS environments
- Never let a vendor’s SOC 2 report substitute for your OQ/PQ—it covers their infrastructure, not your application
- Establish periodic review cycles for SaaS-hosted validated systems; discrete revalidation at cloud velocity is not realistic
- Build your RTM first—if you can’t trace a requirement to a test case, you haven’t validated it
Cloud-hosted validated systems are now the norm in life sciences, not the exception. The frameworks exist, the regulatory guidance has evolved, and the tooling supports it. What’s required is the organizational discipline to do the work—and the understanding that a vendor’s marketing materials about “compliance” are not a substitute for your validation protocols.
References
-
FDA Guidance for Industry: Process Validation: General Principles and Practices. U.S. Food and Drug Administration, January 2011. https://www.fda.gov/media/71021/download
-
ISPE GAMP 5: A Risk-Based Approach to Compliant GxP Computerized Systems, Second Edition. International Society for Pharmaceutical Engineering, 2022. https://ispe.org/publications/guidance-documents/gamp-5
-
ICH Q10: Pharmaceutical Quality System. International Council for Harmonisation, June 2008. https://www.ich.org/page/quality-guidelines
-
FDA 21 CFR Part 11: Electronic Records; Electronic Signatures. Code of Federal Regulations. https://www.accessdata.fda.gov/scripts/cdrh/cfdocs/cfcfr/CFRSearch.cfm?CFRPart=11
-
USP <1058>: Analytical Instrument Qualification. United States Pharmacopeia. https://www.usp.org
-
FDA Guidance: Computerized Systems Used in Clinical Investigations. U.S. Food and Drug Administration, May 2007. https://www.fda.gov/media/70970/download
-
ISPE GAMP Good Practice Guide: IT Infrastructure Control and Compliance. International Society for Pharmaceutical Engineering, 2005.
-
Amazon Web Services: Compliance in Regulated Industries. https://aws.amazon.com/compliance/
-
Microsoft Azure Compliance Documentation. https://docs.microsoft.com/en-us/azure/compliance/
-
FDA Warning Letters Database. https://www.fda.gov/inspections-compliance-enforcement-and-criminal-investigations/warning-letters
Brian Kuzdas is an Enterprise IT Architect with 25+ years of experience specializing in FDA/CGMP validated systems, cloud security, and life sciences technology. Connect on LinkedIn: https://linkedin.com/in/brian-kuzdas-a176b945
#PharmaTech #CSV #ComputerSystemValidation #FDACompliance #CloudComputing #GxP #LifeSciences #QualityAssurance #GAMP5 #21CFRPart11 #CloudSecurity #EnterpriseArchitecture